Global eyes are soon to be turned to the first global football tournament to be held in the Arab world, but malicious actors have already kicked off are World Cup-themed cyberattacks. Email security researchers from the Trellix Advanced Research Center have found attackers to be leveraging FIFA and football-based campaigns to target organizations in Arab countries. It is a common practice for attackers to utilize the important/popular events as a part of the social engineering tactics and particularly target the organizations which are related to event and more promising victim for the attack.
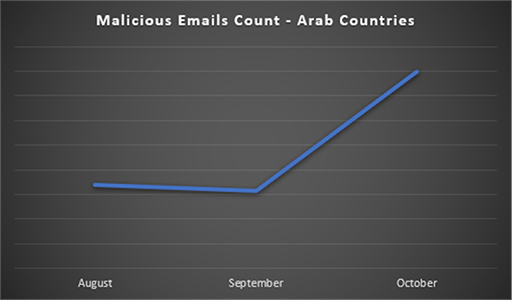
As seen in the above graph, the volume of malicious emails in Arab Countries was observed to have increased by 100% in the month of October. As the host-country and the affiliated organizations prepare for the event, attackers take advantage of employee’s busy schedule which increases the chances of human error and victim interacting with the attack vector. The aim of such attacks can be variable like financial fraud, credential harvesting, data exfiltration, surveillance, or damage to the country’s/organization’s reputation.
Malicious Emails
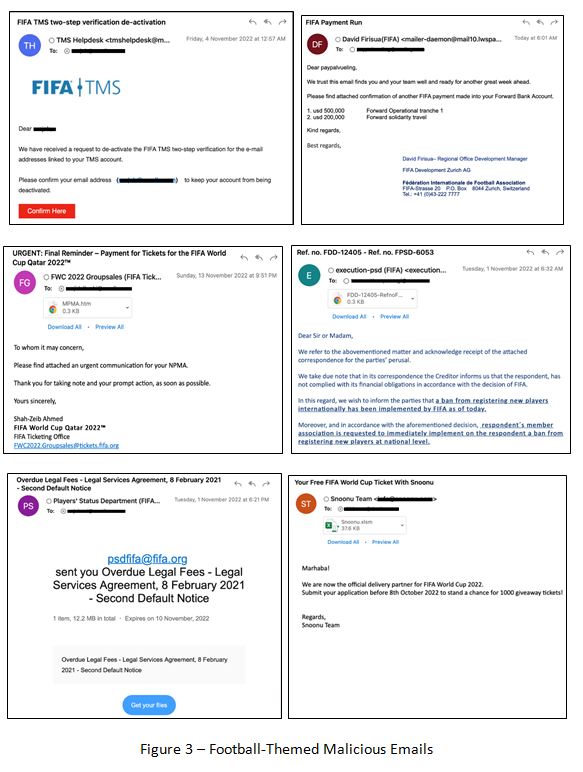
Trellix Advanced Research Center researchers caught various emails utilizing the football tournament as an initial attack vector. The following are cases of samples found in the wild:
- Sample 1: Pretends to be from FIFA TMS helpdesk, and the email body shows a fake alert notification regarding the de-activation of two factor authentication and contains a hyperlink which redirects the user to a phishing page.
- Sample 2: Attempts to impersonate David Firisua, the team manager for Auckland City FC, and seeks confirmation of a payment made to the receiver’s account in reference to FIFA. It also contains a hyperlink to a customized phishing page of trusted brand.
- Sample 3: Impersonates the FIFA ticketing office and conveys a payment issue for the victim to urgently resolve. It also contains a html attachment which redirects the user to a customized phishing page.
- Sample 4: A fake legal notification informing the recipient about a ban implemented by FIFA from registering new players to create a sense of urgency. It also contains a html attachment which redirects the user to a customized phishing page.
Sample 5: A fake file notification set in the WeTransfer’s template. It attempts to impersonate the Players Status Department and send victims a legal notice regarding delayed legal fees. It contains a link which redirects the user to a malicious website either delivering malware or hosting a phishing page.
Malicious URLs
Malware
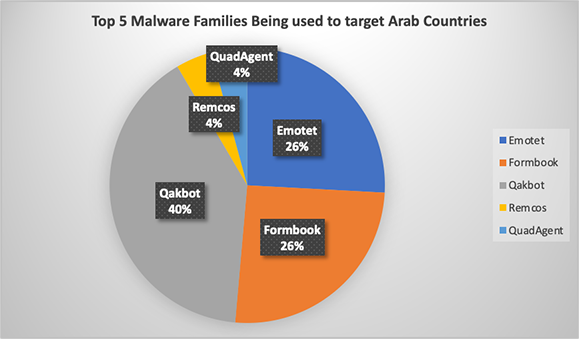
Trellix solutions have identified several malware families being used to target Arab countries. The top five malware families based on the volume of the attacks include:
- Qakbot: An information stealer and banking Trojan with backdoor capabilities. It inserts malicious replies into the middle of existing email conversations, using the compromised accounts of other infection victims.
- Emotet: An advanced Trojan primarily spread via phishing email attachments and links that, once clicked, launch a payload. The goal is to access foreign devices and spy on sensitive confidential data.
- Formbook: An infostealer malware which is used to steal several types of data from infected systems, including credentials cached in web browsers, screenshots, and keystrokes. It can also act as a downloader, enabling it to download and execute additional malicious files.
- Remcos: A Remote Access Software used to remotely control computers, once installed, opens a backdoor on the computer, granting full access to the remote user.
- QuadAgent: A PowerShell backdoor, and another tool used by the OilRig group to perform attacks on targeted machines.
Indicators of compromise
The following link contains examples of malicious URLs, binaries and email addresses used in the recent campaigns targeting Arab Countries.
Trellix protection
Trellix Email Security provides reliable detection from such campaigns by preventing emails from ever reaching your system. In addition, Trellix also detects campaigns on other levels like network, URL and binary to provide complete protection to our customers.
The following are some of the many rules authored by us to detect such campaigns:
- FE_Trojan_HTM_Phish_246
- Phishing_Null_Content_33
- Phishing_Qbot
- Phishing_Qbot_Zip_Expiry
Conclusion
As the much-awaited football tournament comes close, cybercriminals are expected to leverage every opportunity they get to capitalize on news trends, ticket demands, human errors due to the busy schedule and more in order to deliver a cyberattack. We anticipate these attacks to continue through January 2023 and would advise everyone to stay vigilant of any attack vectors. The organizations which are directly related to the event are advised to stay extra-vigilant as they would be the most promising targets for such attacks.This document and the information contained herein describes computer security research for educational purposes only and the convenience of Trellix customers. Trellix conducts research in accordance with its Vulnerability Reasonable Disclosure Policy.
Any attempt to recreate part or all of the activities described is solely at the user’s risk, and neither Trellix nor its affiliates will bear any responsibility or liability.